Who This Is For
This guide is not for single-user local laptop installs. It is for a 30-day trial of OpenHands Enterprise on a dedicated VM/server on your own infrastructure. The deployment requires DNS records, network, and compute setup before installation. If you want to use OpenHands immediately without infrastructure setup:- Use OpenHands Cloud (SaaS)
- Run OpenHands open-source locally using Docker, CLI or SDK
Accounts and Credentials
Before you begin, make sure you have the following ready:- Anthropic API key from the Anthropic Console
- A GitHub account with permission to create GitHub Apps
- An AWS account with permissions to create EC2, VPC, and Route53 resources (if using the AWS with Terraform path)
Provision Infrastructure
You will need a VM to host OpenHands Enterprise. Choose one of the options below to provision your infrastructure.- AWS with Terraform (Recommended)
- Manual VM Setup
We provide a Terraform module that provisions a properly configured environment
for OpenHands Enterprise, including the EC2 instance, DNS records, and TLS certificates.
OpenHands AWS Terraform Module
Follow the README instructions to configure and apply the Terraform configuration.
Preflight Validation
All items below must be completed before running the installer:- VM meets CPU, memory, disk, and OS requirements
- DNS records are created and resolve from the VM
- Inbound ports are open:
80,443, and30000 - Outbound domains are reachable from the VM
- GitHub App prerequisites are prepared
DNS checks
Run the checks below on the target VM before opening the installer dashboard. Export your base domain:test.runtime.${BASE_DOMAIN} resolves to the same target as ${BASE_DOMAIN}.
Outbound connectivity checks
000 is acceptable for reachability checks
(for example 200, 301, 302, 401, 403, 405).
If any check fails, stop and resolve before continuing:
- DNS failures: Verify records are created, point to the right target, and have finished propagating
- Outbound connectivity failures: Check firewall egress rules, proxy settings, and TLS inspection policies
Reasons for Requirements
| Requirement | Why It Exists |
|---|---|
443/TCP inbound | Primary HTTPS entrypoint for users and service hostnames |
30000/TCP inbound | Replicated/KOTS Admin Console for install and configuration |
80/TCP inbound | HTTP entrypoint used for ingress/redirect behavior |
*.runtime.<domain> DNS + cert SAN | Runtime sandboxes are addressed by dynamic runtime-specific hostnames |
replicated.app, proxy.replicated.com | Replicated control-plane/license/install paths |
images.r9..., charts.r9..., updates.r9..., install.r9... | Vendor distribution image/chart/update/install endpoints |
traefik.github.io | Embedded cluster ingress chart repository |
ghcr.io, registry-1.docker.io | Container image pulls for platform components |
github.com | GitHub App setup/auth/webhooks and downloading public agent skills |
Run the Installer
1. Access the Installer Dashboard
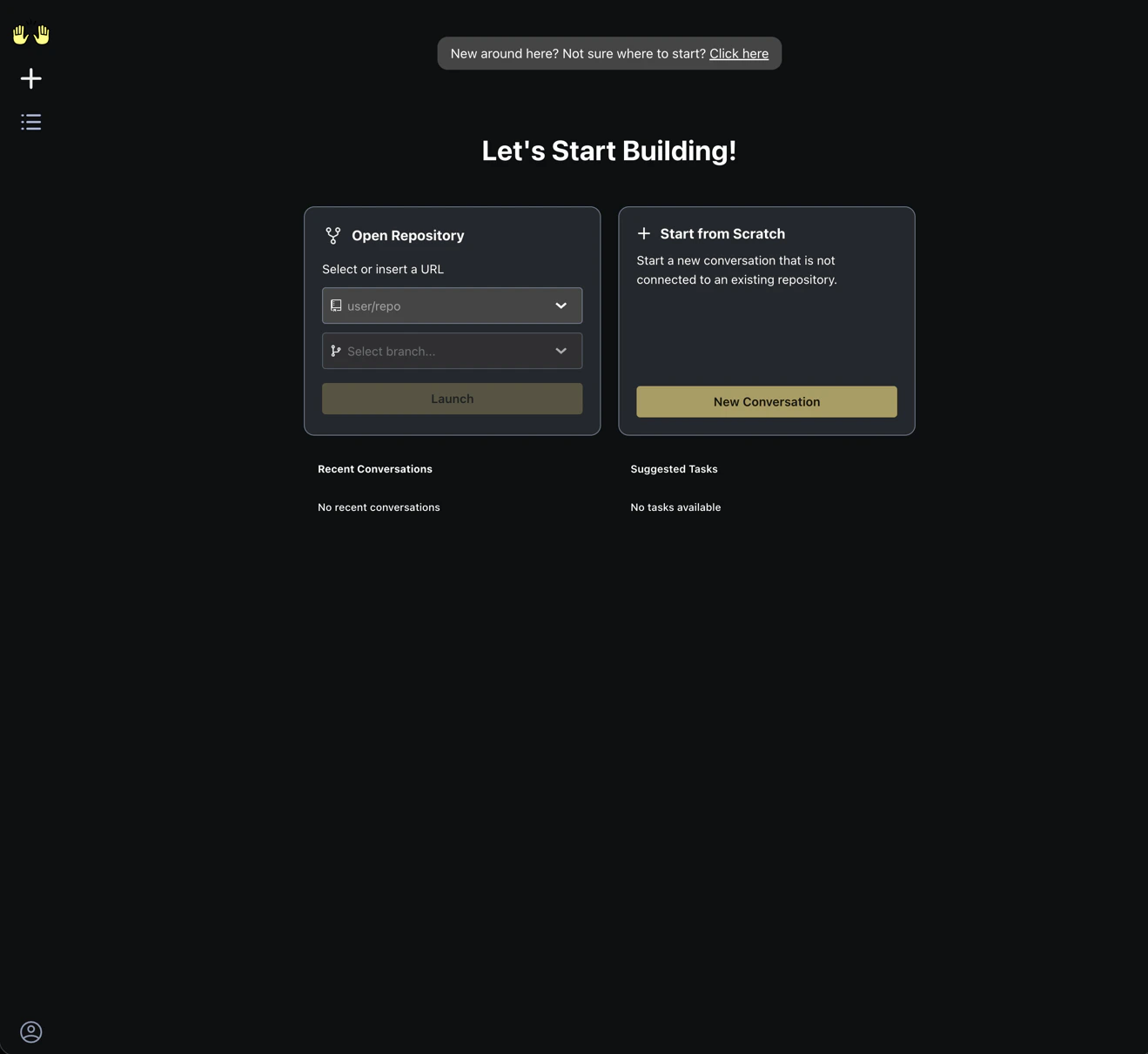
After preflight validation checks have passed, register for a free 30-day trial, then log in to the installer dashboard. You will see the dashboard below. Click “View install guide” in the Install tile.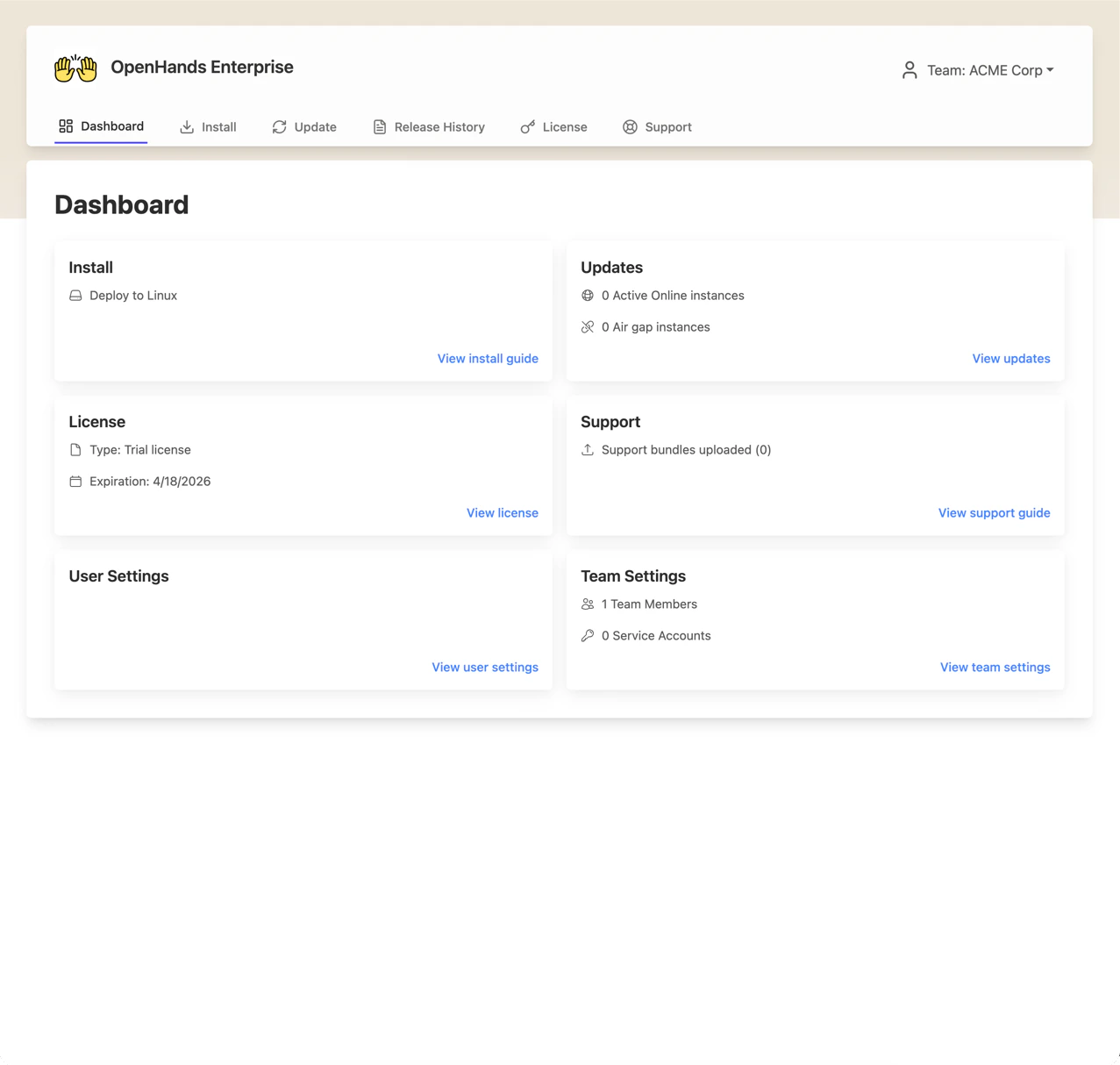
2. Name your instance
Enter a name for your instance (e.g., your company name or environment identifier). Select “Outbound requests allowed” for Network Availability, then click Continue.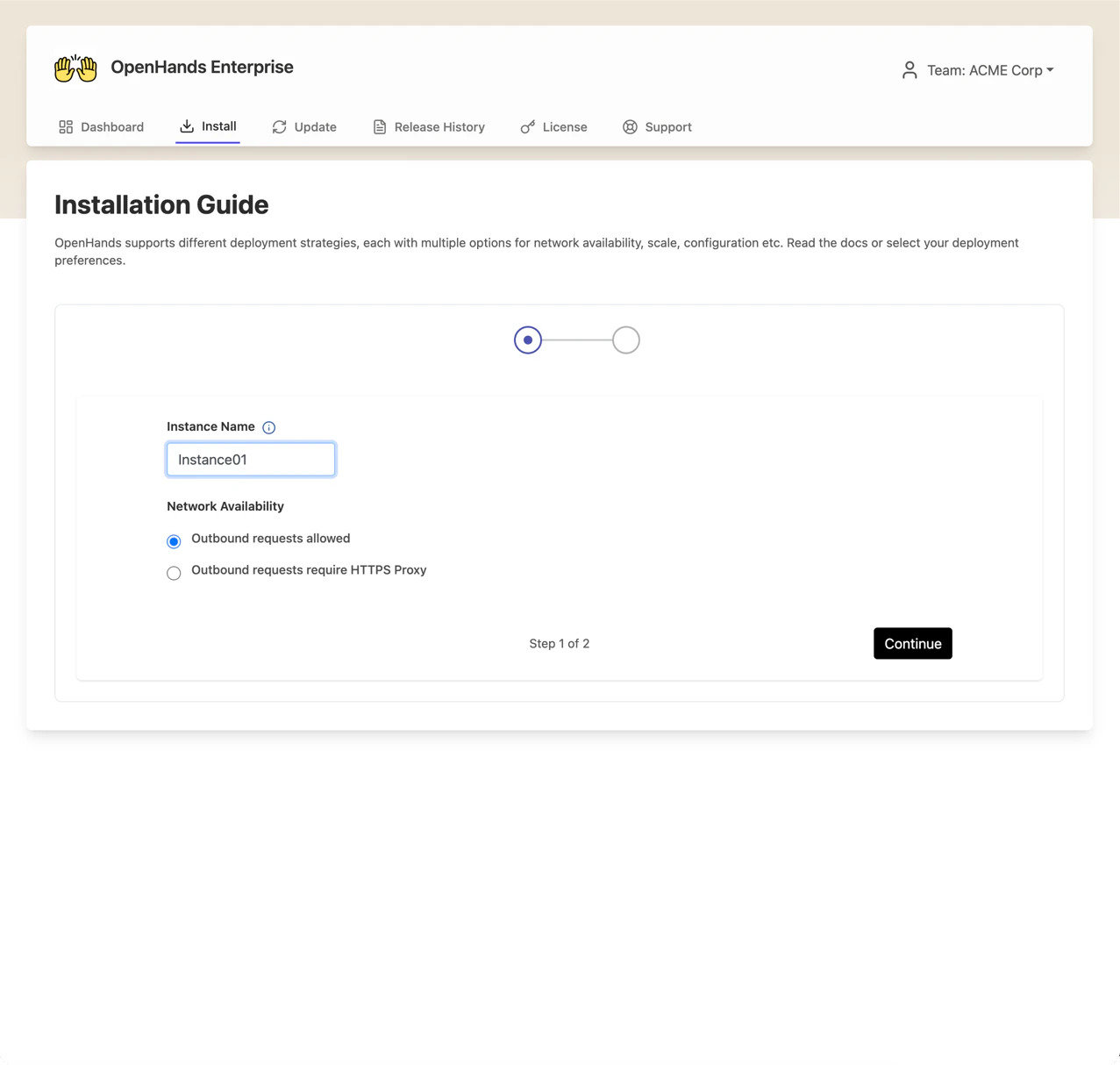
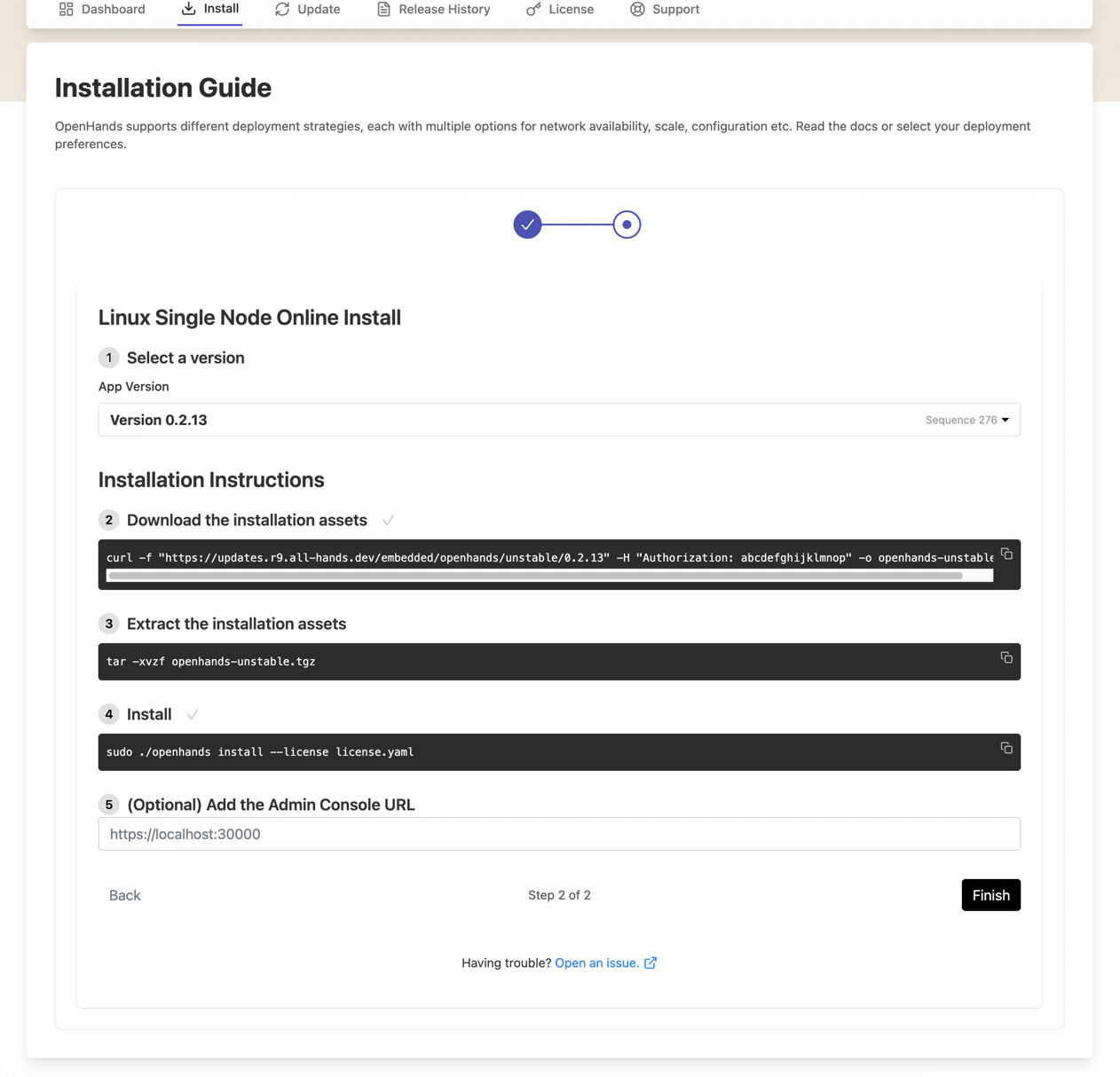
3. Run the installation commands
The install guide provides commands to run on your VM. SSH into your VM and execute them in order:- Select a version — the latest version is pre-selected
- Download the installation assets — copy and run the
curlcommand shown - Extract the installation assets — run the
tarcommand shown (this includes your license file) - Install — run the install command shown
sudo ./openhands support-bundle and share the resulting bundle with support.
4. Access the Admin Console
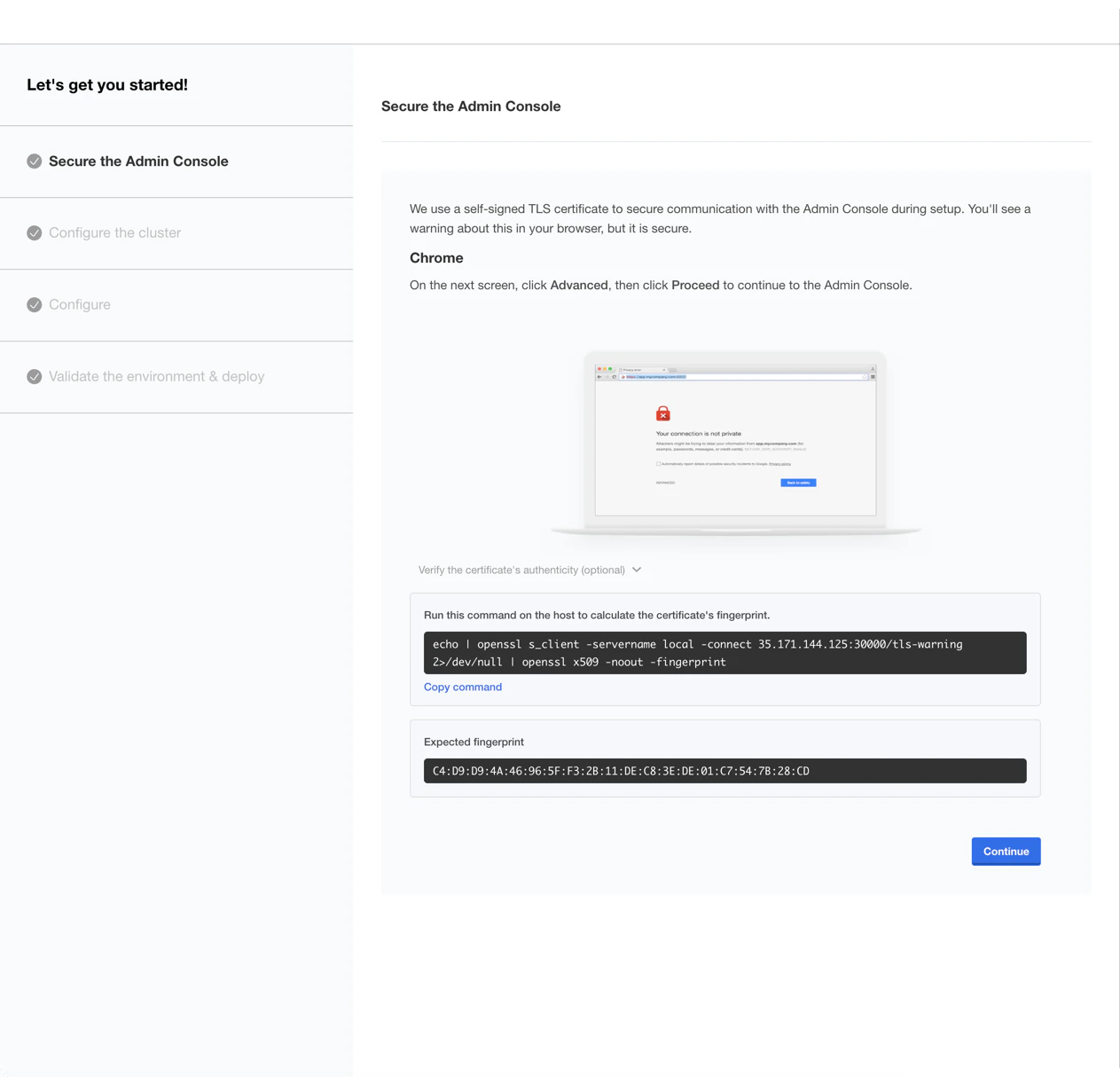
Once the install command completes, the Admin Console is available at:https://<your-base-domain>:30000(if you provided TLS certificates)http://<your-vm-ip>:30000(if you did not use the--tls-certand--tls-keyflags on theinstallcommand)
install command, your browser will display a security warning.
Click Advanced, then Proceed to continue to the Admin Console.
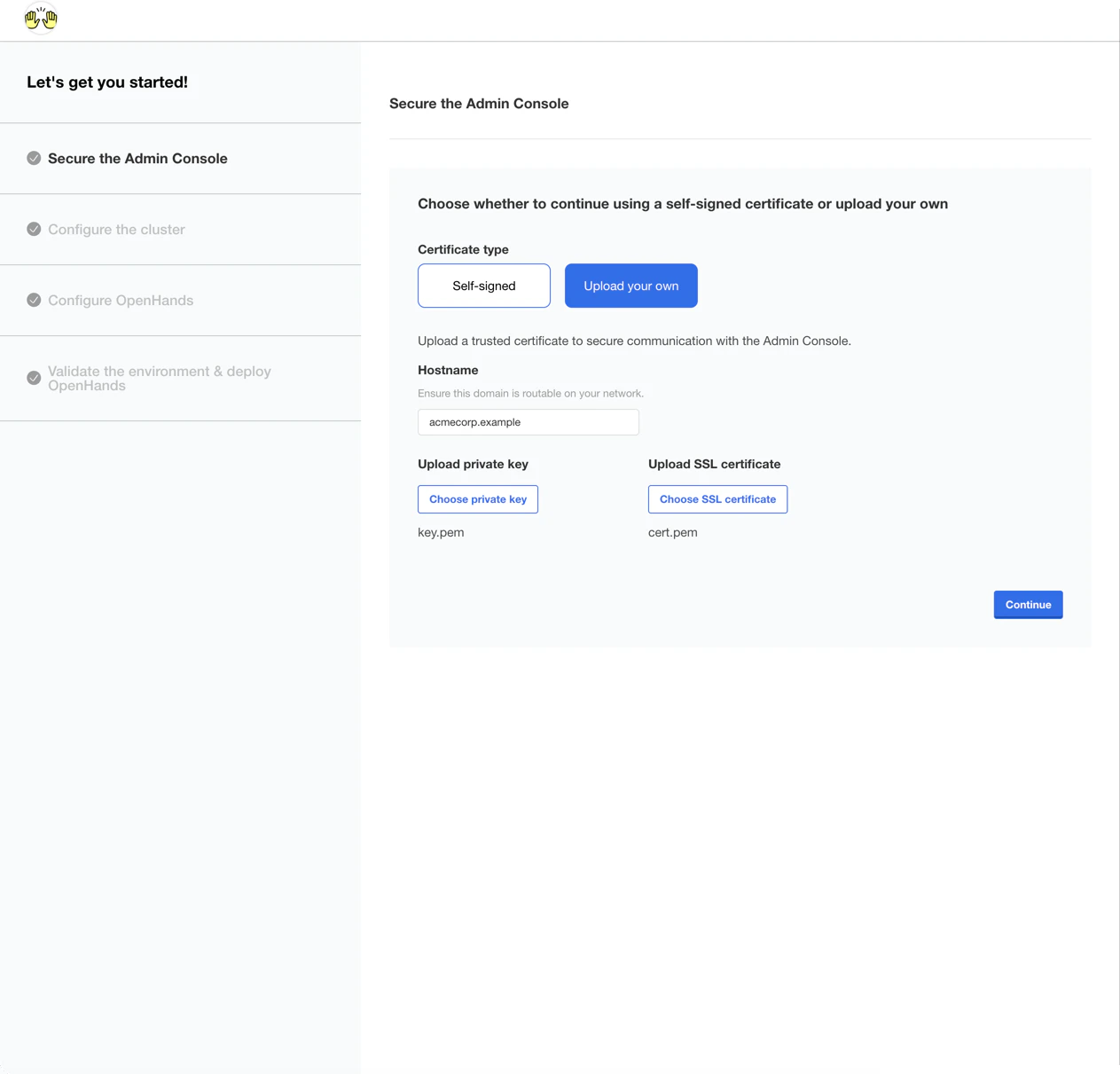
5. Upload TLS certificate (if not provided with the install command)
If you did not provide certificates with theinstall command, select “Upload your own”,
enter your base domain under Hostname, upload your private key and SSL certificate, then click Continue.
6. Log in to the Admin Console
Enter the password you set during installation and click Log in.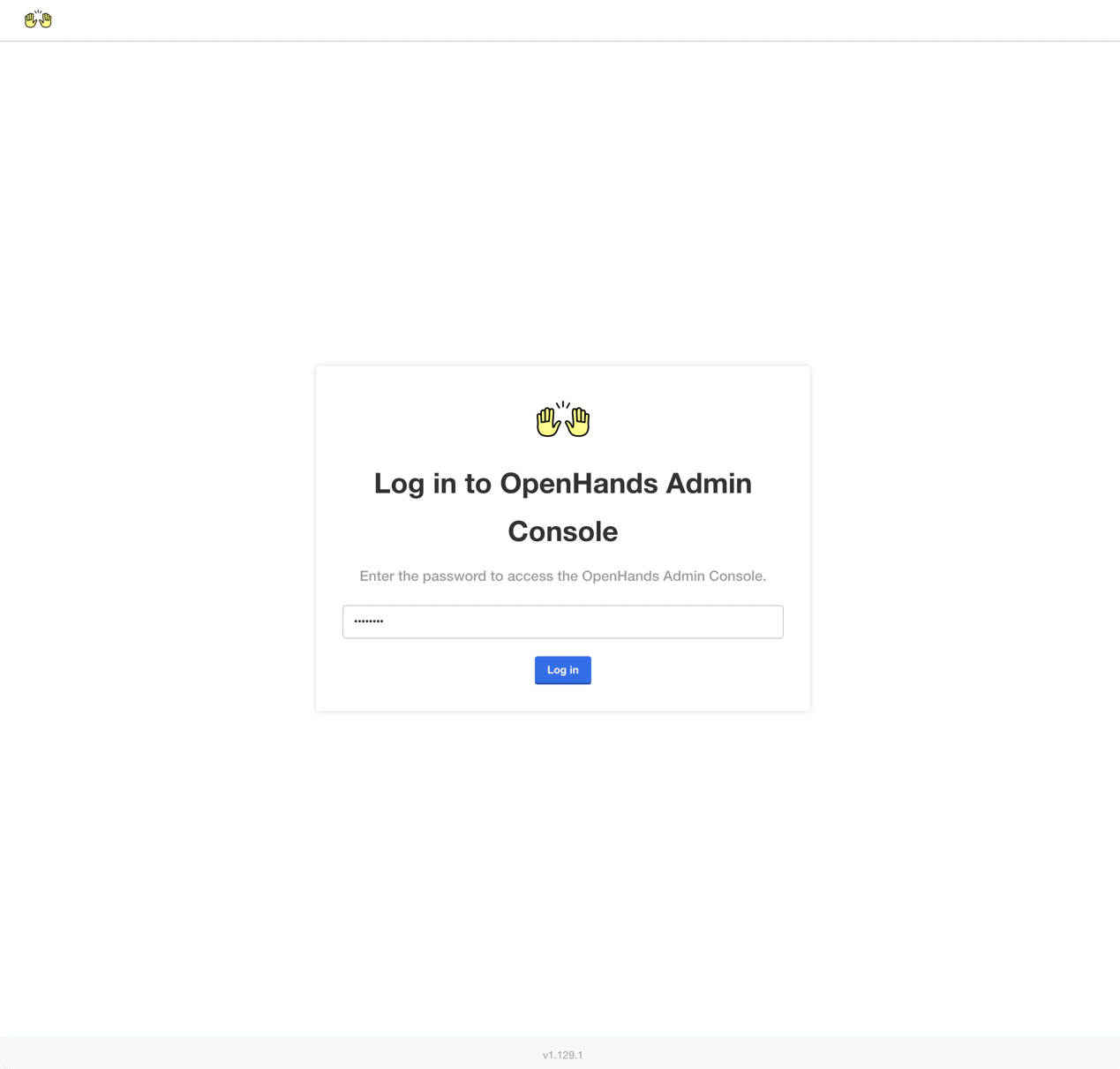
7. Configure the cluster
You will be prompted to add additional nodes to the cluster. For a single-node deployment, click Continue to skip this step.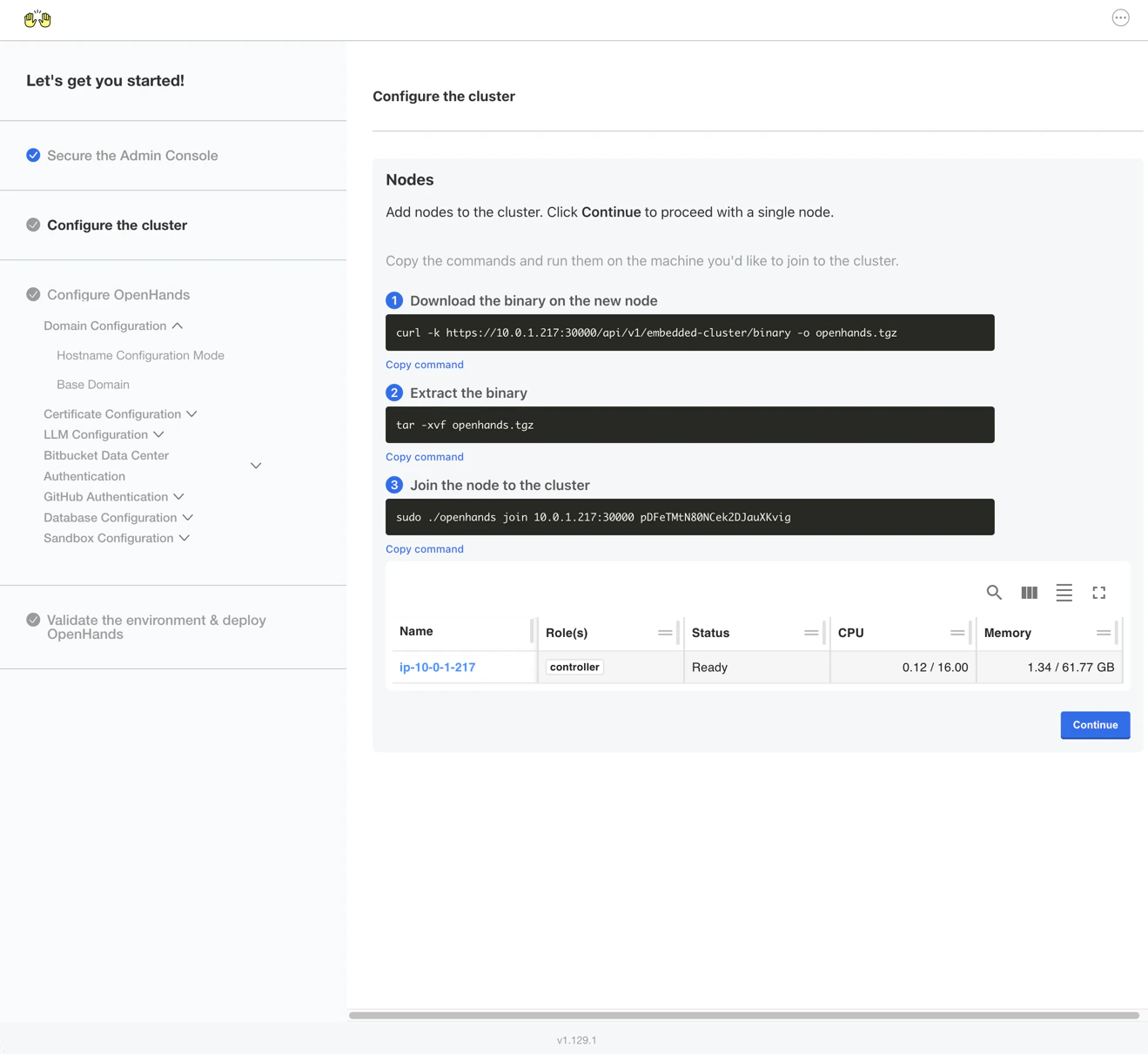
Configure OpenHands
You should now see the application configuration page.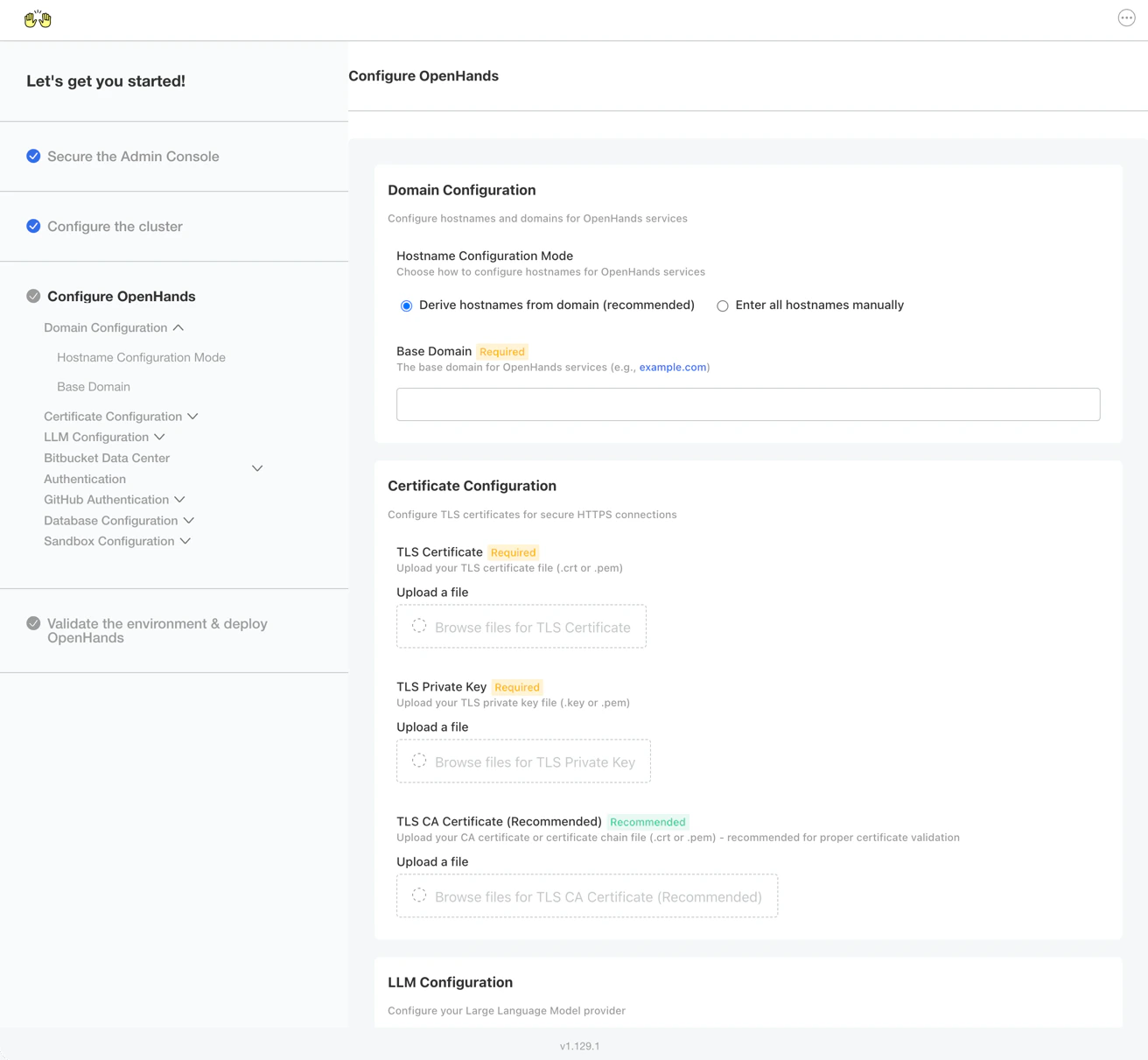
Domain Configuration
- Select “Derive hostnames from domain (recommended)”
- Enter your base domain (e.g.,
openhands.example.com)
Certificate Configuration
- Upload your TLS Certificate (
.crtor.pem) - Upload your TLS Private Key (
.keyor.pem) - Optionally upload the root CA Certificate for your TLS certificates
LLM Configuration
Enter your Anthropic API key from the Anthropic Console.GitHub Authentication
Enable GitHub Authentication in the Admin Console, then follow these steps to create and configure a GitHub App.Create a GitHub App
- Go to github.com/settings/apps and click New GitHub App.
-
Set a unique GitHub App name (e.g.,
ACME Corp OpenHands). -
Set the Homepage URL to
https://app.<YOUR_BASE_DOMAIN>. -
Under Identifying and authorizing users:
- Set the Callback URL to:
- Check the box for Request user authorization (OAuth) during installation
- Set the Callback URL to:
-
Under Webhook:
- Set the Webhook URL to:
- Generate a webhook secret:
- Paste the generated value into the Secret field
- Set the Webhook URL to:
-
Under Permissions, configure the following:
Repository permissions:
Organization permissions:
Permission Access Actions Read and write Commit statuses Read and write Contents Read and write Issues Read and write Pull requests Read and write Webhooks Read and write Workflows Read and write Account permissions:Permission Access Events Read-only Permission Access Email addresses Read-only - Click Create GitHub App.
- On the GitHub App page, under Client secrets, click Generate a new client secret. Save this value.
-
Under Private keys, click Generate a private key. The
.pemfile downloads automatically — note its location.
Map GitHub App values to Admin Console
Go back to the Installer Admin Console in your browser and enter the following values:| GitHub App Value | Admin Console Field |
|---|---|
| Client ID (shown on app page) | GitHub OAuth Client ID |
| Client secret (from step 8) | GitHub OAuth Client Secret |
| App ID (shown on app page) | GitHub App ID |
| Webhook secret (from step 5) | GitHub App Webhook Secret |
| Private key file (from step 9) | GitHub App Private Key (file upload) |
Deploy and Verify
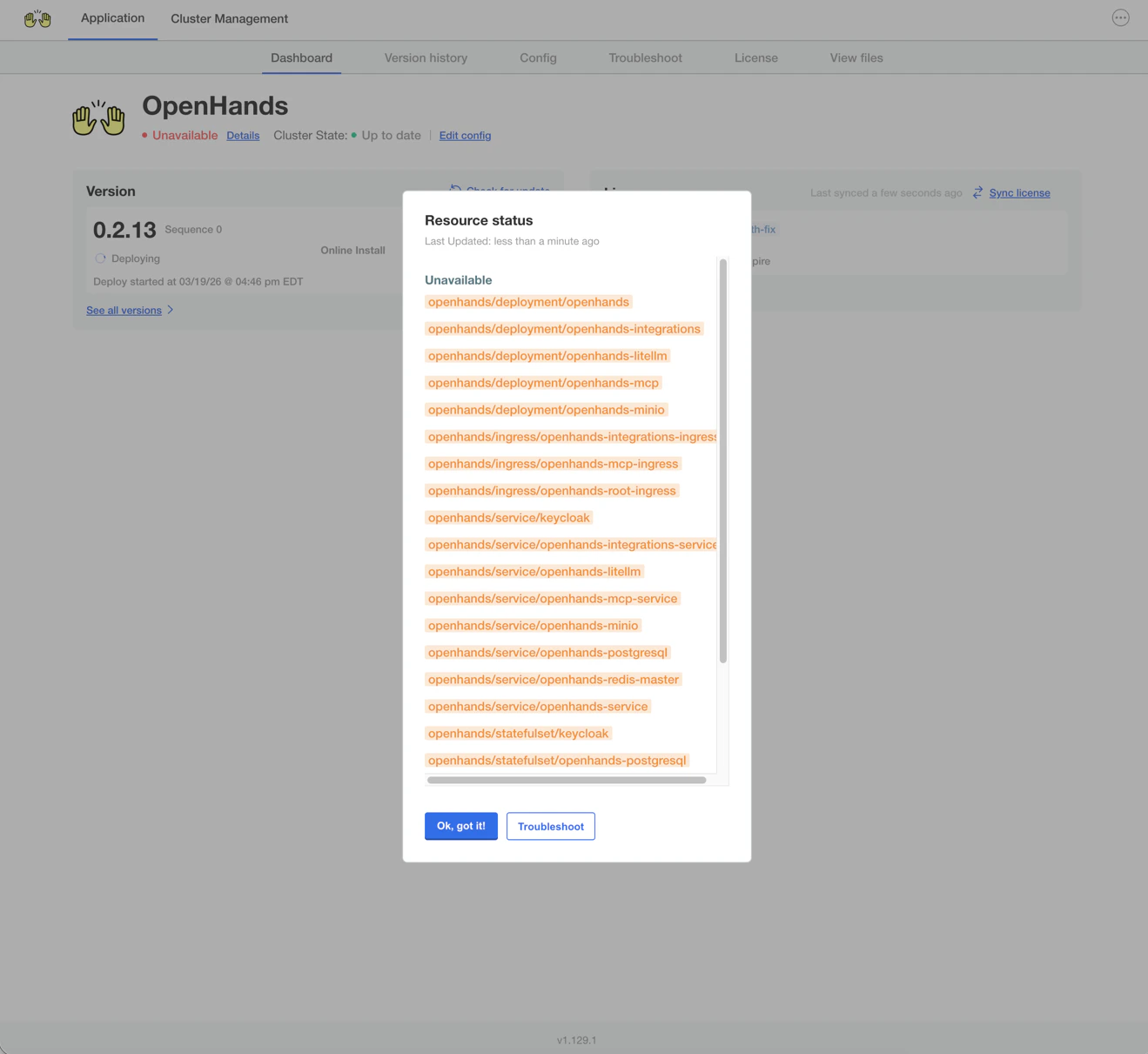
OpenHands will begin deploying. You can expect the deployment status to transition from Missing to Unavailable to Ready. This typically takes 5-10 minutes.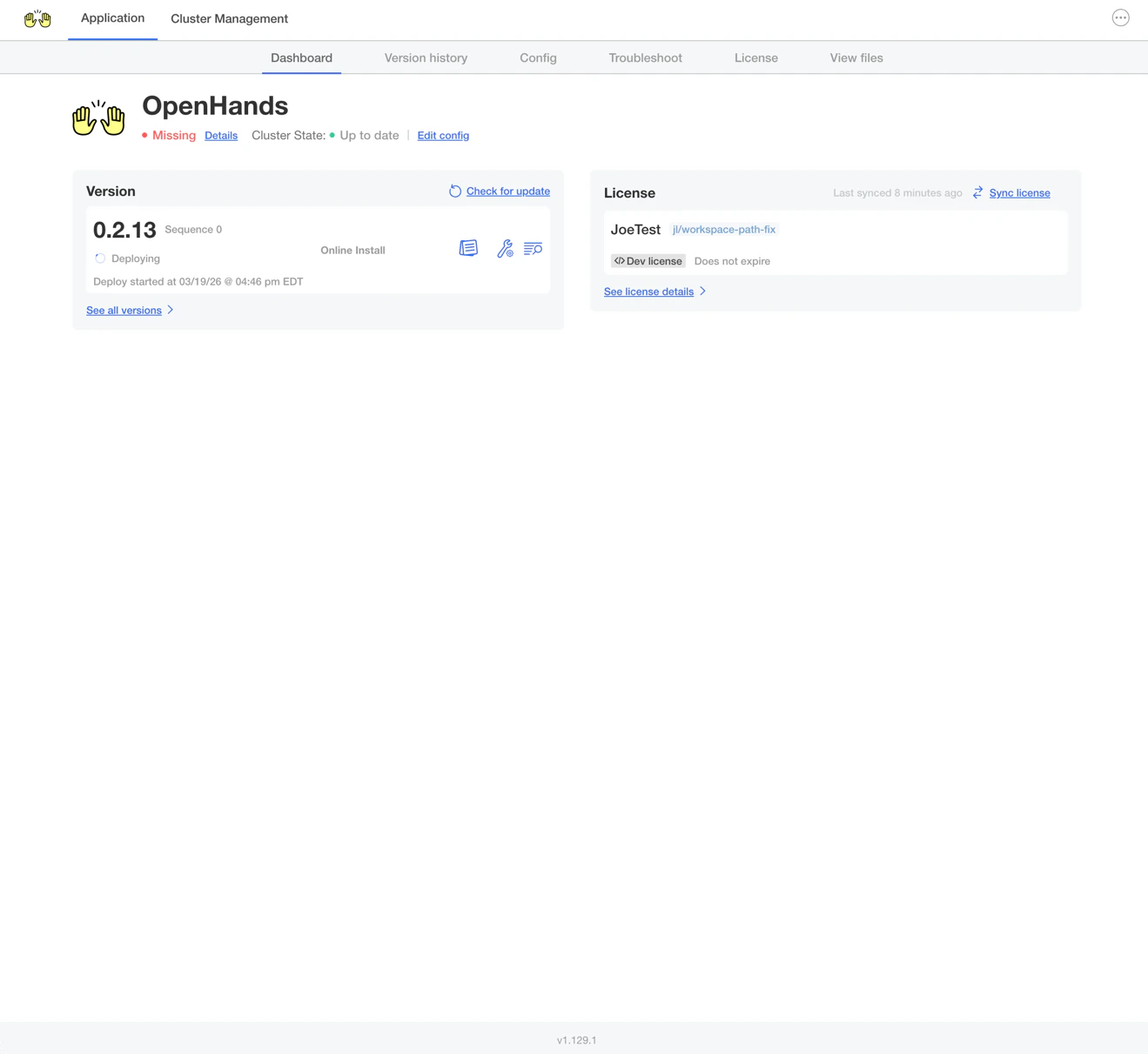
First Login
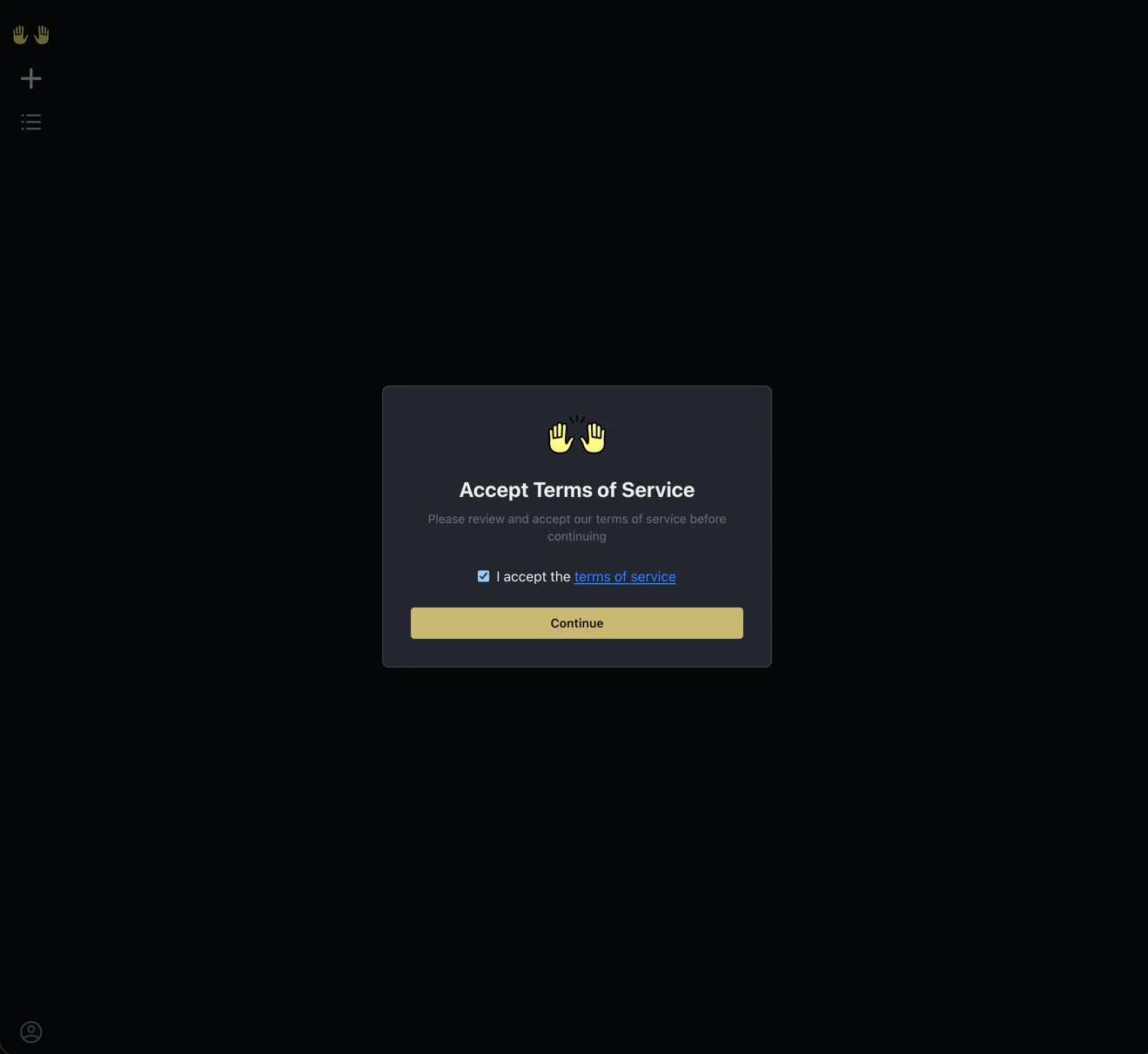
Once the deployment status shows Ready, navigate tohttps://app.<your-base-domain>
and click the Login with GitHub tile.
Accept the Terms of Service and click Continue.
Next Steps
Enterprise Overview
Learn about OpenHands Enterprise features, integrations, and deployment options.
Prompting Best Practices
Get the most out of your AI coding agents with effective prompting techniques.
Contact Support
Reach out to the OpenHands team for deployment assistance or questions.
OpenHands Documentation
Explore the full OpenHands documentation for usage guides and features.